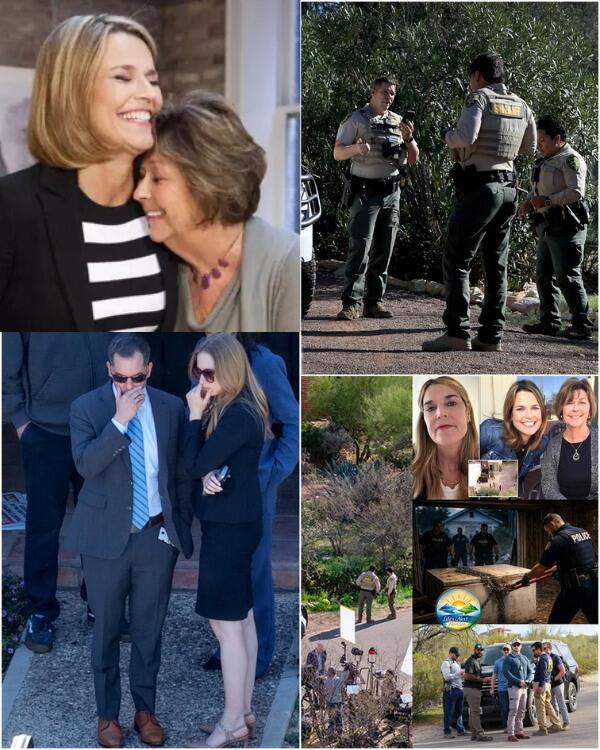
In recent days, public opinion has been drawn to a shocking scenario surrounding the so-called “cage photo,” which allegedly mysteriously appeared inside the Guthrie mansion. According to information circulating on social media, a printer in the house unexpectedly activated in the middle of the night, printing an image of Nancy trapped in a cage on a ship, along with a demand for a $50 million ransom before dawn. The story even went further, mentioning an emergency signal jamming operation and investigators tracing the source from a “secret room.” However, when these details are viewed through a legal and technical lens, the picture becomes far from its initial dramatic appearance.
First, there has been no official confirmation from law enforcement agencies regarding the existence of such a photo. In actual kidnapping cases, information related to ransom and photographic evidence is usually kept confidential to facilitate investigations. The fact that a printing device “activated itself” in the middle of the night, if it happened, could be entirely explained by technical factors: a print job stuck in memory, unauthorized access via an unsecured Wi-Fi network, or even a deliberate hoax designed to create a psychological effect.
It’s important to emphasize that the $50 million ransom demand is unrealistic in the context of typical extortion cases. Demands exceeding the ability to pay are often more symbolic than practical, aimed at causing panic or attracting media attention. Meanwhile, professional criminal groups – if any – usually consider the actual ability to pay to maximize their chances of receiving the money. The “impossibility” of this figure is one of the signs that this may be fabricated or exaggerated information.
The “ship at sea” element in the photo also needs careful consideration. Some posts suggest that details in the “Guthrie Mansion Digital Audit Report 2026” indicate that the object in the photo is not a ship offshore, but a landmark visible from the attic of the house. However, no publicly available documents confirm the existence of such a report. In official investigations, digital audit records are typically sealed and only released when necessary in court.
The hypothesis of signal tracing and emergency jamming deployment also raises many questions. Telecommunications jamming in the United States is strictly controlled by federal law and is only permitted under exceptional circumstances with explicit approval. Describing such an operation as occurring instantaneously overnight, based on an unverified printout, is unlikely to fit the standard procedures of an investigative agency.

Even more noteworthy is the mechanism by which the story spread. In the social media environment, details like “automatic printer,” “iron cage on a ship,” or “secret room” are highly appealing because they tap into collective fear and imagination. When unverified information is repeated sufficiently, it can create the illusion of authenticity. This phenomenon has been observed in many disinformation campaigns, where dramatic effect is prioritized over credibility.
From a digital investigation perspective, if an unusual printout actually appears, the logical step would be to analyze device logs, access the router, and identify the associated IP address. This process is highly technical and time-consuming, not something that can be done in a few hours. Cybersecurity experts often emphasize that most “mysterious” incidents involving home devices stem from weak configurations or insecure network intrusions.
Legally, publicly releasing an image allegedly showing a victim being held captive, without verification, can cause serious harm to the family and hinder the investigation. In many cases, authorities have to urge the public not to share unverified content to avoid creating pressure or spreading misinformation.
The detail that the “ship” was actually a landmark visible from the attic further suggests the possibility of staging. If someone wanted to create the impression that the victim was far out at sea, using a familiar image within the local field of vision and then editing the background is a simple technique. Current photo editing technology allows for background merging and adding details with a high degree of realism, enough to deceive non-expert viewers.
The crucial point in such situations is to distinguish between official information and speculation. To date, no investigative agency has confirmed the $50 million ransom demand or the discovery of the “secret room.” What exists is primarily viral posts, lacking sources and relying more on emotion than evidence.
In the context of a sensitive case, public and media caution is crucial. History shows numerous instances where rumors exerted undue pressure, wasted investigative resources, and even endangered potential victims. Conversely, waiting for confirmed information, albeit slower, is the only way to ensure accuracy and fairness.
The story of the “photo-stacked” image
The term “ironclad” can therefore be seen as a test of society’s resilience to unverified information. It raises questions not only about technology and security, but also about individual responsibility when sharing shocking content. In an age where a single click can amplify information to millions, prudence becomes the minimum requirement.
Until official confirmation from authorities, any details regarding the ransom, the ship, or the jamming campaign should be considered hypothetical. Criminal investigations don’t operate like a movie script; they rely on evidence, procedures, and independent verification. And while the truth may take time to emerge, it is the public’s responsibility not to be swept away by sensational but unsubstantiated stories.
Để lại một bình luận